Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
The enterprise cybersecurity landscape in 2026 is more complex and consequential than ever before. With global cybercrime damages projected to exceed $10.5 trillion annually, organizations across every industry face threats that are growing in sophistication, frequency, and financial impact. From ransomware campaigns targeting critical infrastructure to state-sponsored espionage operations, the pressure on IT security teams has never been greater.
For enterprises in Manufacturing, Healthcare, Telecom, Finance, and Government, a proactive and layered approach to cyber threat protection is no longer optional. It is a business imperative. In this guide, we explore the most pressing cybersecurity threats of 2026, emerging trends reshaping defense strategies, and the cybersecurity best practices every enterprise should adopt today.
Ransomware remains the single most disruptive cyber threat facing enterprises in 2026. What has changed is the level of precision and planning behind modern attacks. Threat actors now conduct weeks or months of reconnaissance before deploying payloads, targeting backup systems, supply chain partners, and cloud environments simultaneously to maximize pressure on victims.
Key ransomware trends enterprises must address include:
Effective ransomware defense requires immutable backups, network segmentation, endpoint detection and response (EDR), and rigorous incident response planning tested through regular tabletop exercises.
The traditional perimeter-based security model, built on the assumption that everything inside the corporate network can be trusted, has proven inadequate for the modern enterprise. Zero trust architecture has emerged as the defining framework for enterprise cybersecurity in 2026.
Zero trust operates on a fundamental principle: never trust, always verify. Every user, device, and application must continuously prove its identity and authorization before accessing any resource, regardless of its location on or off the network.
Enterprises that partner with experienced IT security services providers can accelerate their zero trust journey by leveraging proven architectures, integration expertise, and ongoing managed security operations.
Artificial intelligence and machine learning have transformed how enterprises detect, analyze, and respond to cyber threats. In 2026, AI-powered security tools are no longer experimental; they are essential components of any mature security operations center (SOC).
However, enterprises must also recognize that adversaries are using AI to enhance their own attacks, including AI-generated phishing emails, deepfake-based social engineering, and automated vulnerability scanning. A robust AI defense strategy must account for these adversarial applications.
Regulatory compliance has become a central driver of enterprise cybersecurity investment. Organizations operating across multiple jurisdictions must navigate an increasingly complex web of data protection laws, industry-specific regulations, and security standards.
Compliance is not security, but it provides a structured foundation. Enterprises should treat regulatory requirements as a baseline and build additional controls based on their specific risk profile, industry threats, and business objectives.
Technology alone cannot protect an enterprise. Human error remains a contributing factor in the majority of data breaches, with phishing, credential misuse, and misconfigured systems among the most common root causes. A strong cybersecurity culture, built through consistent and engaging employee training, is indispensable.
Organizations that invest in their people as the first line of defense see measurable reductions in successful social engineering attacks and faster identification of potential breaches.
Enterprise cybersecurity in 2026 demands a holistic strategy that integrates technology, process, and people. No single tool or framework is sufficient on its own. Success requires continuous adaptation, deep expertise, and the ability to operationalize security across complex, distributed environments.
At Super Express, we bring over 10 years of experience delivering IT security services and comprehensive technology solutions to more than 50 clients across 15+ countries. With 150+ successful projects spanning SAP, AI/ML, Cloud, IoT, DevOps, and cybersecurity, our team understands the unique challenges facing enterprises in Manufacturing, Healthcare, Telecom, Finance, and Government.
Whether you need to implement a zero trust architecture, deploy AI-powered threat detection, achieve compliance with evolving regulations, or build a security-aware workforce, Super Express provides the expertise and partnership to protect your enterprise against the threats of today and tomorrow.
Ready to strengthen your enterprise cybersecurity posture? Contact Super Express today to schedule a consultation with our security experts and take the first step toward a more resilient future.
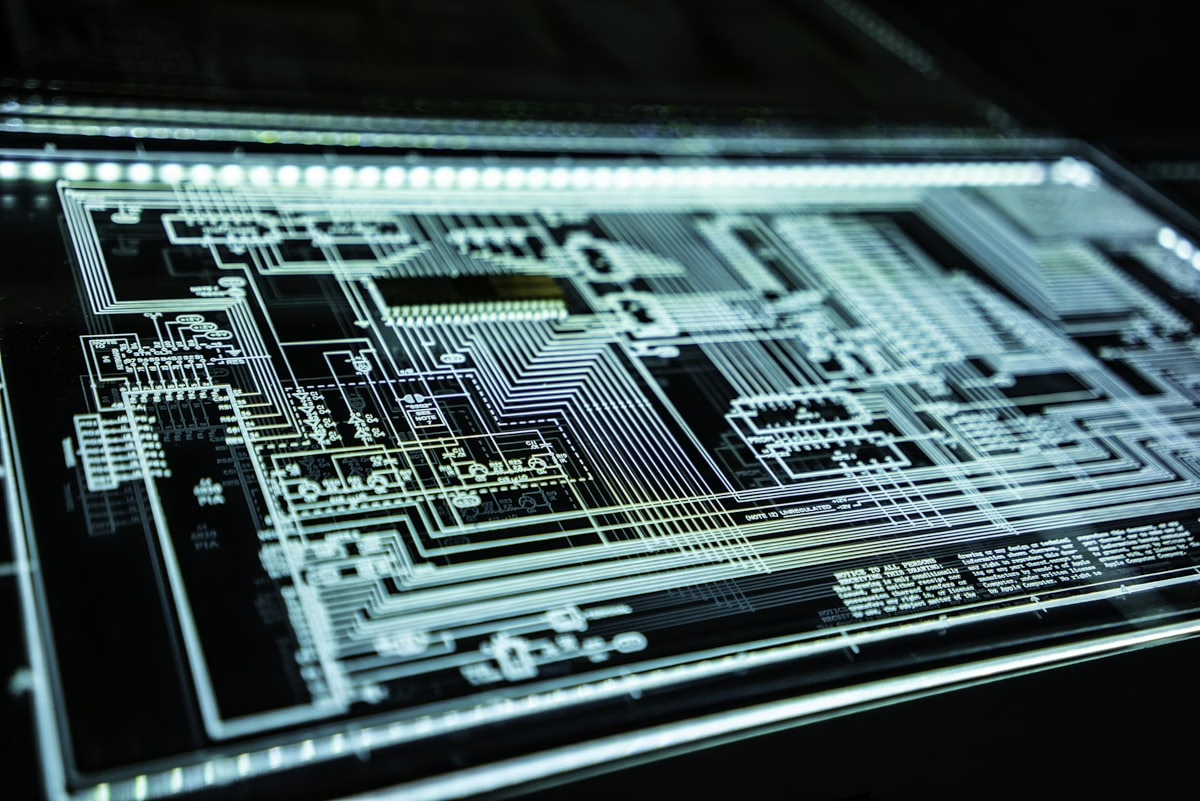
Featured image via Unsplash